Cyber-attacks have become so rampant these days. Small and medium organizations and businesses have suffered greatly from the offenders of this attack.
Cyber Security landscape has intervened by trying to curb cyber-attacks by providing open-source cybersecurity projects to fortify the data breaches that afflicted companies, which leads to their bankruptcy because of financial and reputation losses.
On this page, we will be addressing some important Opensource Cybersecurity projects. Follow us as we take you on a nice ride.
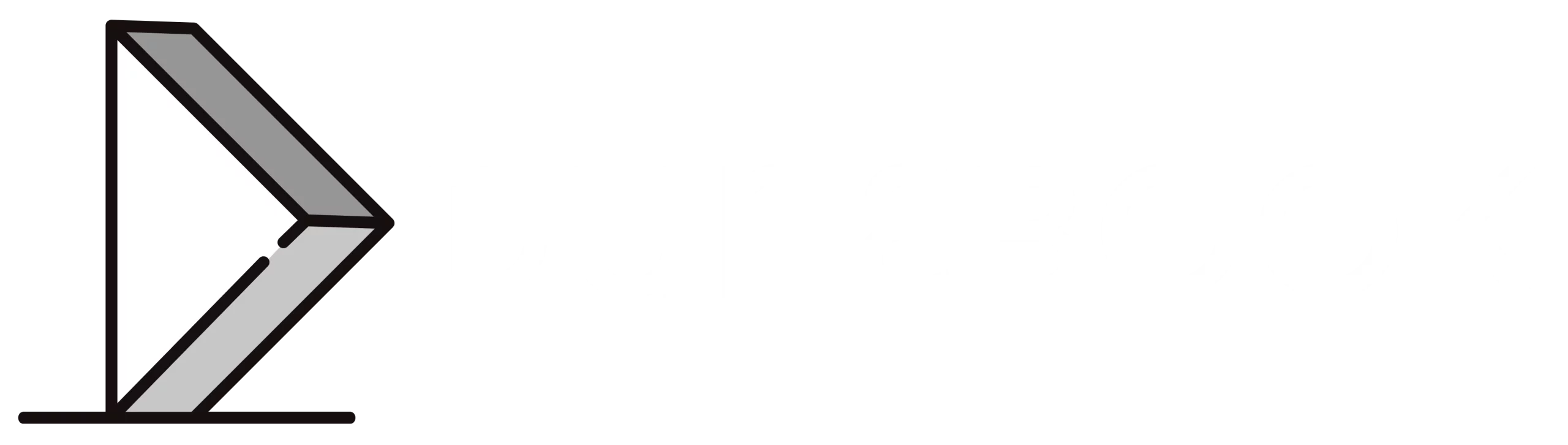
1. Vuls
Vuls is known as Vulnerability Scanner. Linux, FreeBSD, Container Image, Running Container, WordPress, Programming language libraries, Network devices make use of this security.
Secondly, It updates you on servers that are affected and it also automatically detects Vulnerabilities in order to guild against unforeseen circumstances
Lastly, with the help of this Open source cybersecurity project, you get to know Vulnerabilities that are concerned with the system in use.
More information2. Lockdoor Framework
LockDoor is a Framework aimed at helping penetration testers, bug bounty hunters And cybersecurity engineers.
This tool is designed for Debian/Ubuntu/ArchLinux based distributions to create a similar and familiar distribution for Penetration Testing.
But containing the favorite and the most used tools by Pentesters.

3. H4cker
A lot of resources having to do with ethical hacking (penetration testing), digital forensics and incident response (DFIR), vulnerability research, exploit development, etc. are found in this open-source cybersecurity project.
These resources are there to provide you with good guidance on how to play safely. It is being managed by Omar Santos.
This open-source cybersecurity project got in store for you more than 7,000 references, scripts, tools, code, and other resources to help you in knowing and developing new skills to fight against cyber attacks.
4. Awesome Incident Response
This project is to assist Digital Forensics and Incident Response (DFIR) teams and security analysts in organizations with a well managed and organized collections of tools and resources for security incident response.
Noting that DFIR teams in every organization do collect and correct incidents, and also implement controls to guild against them in the future.

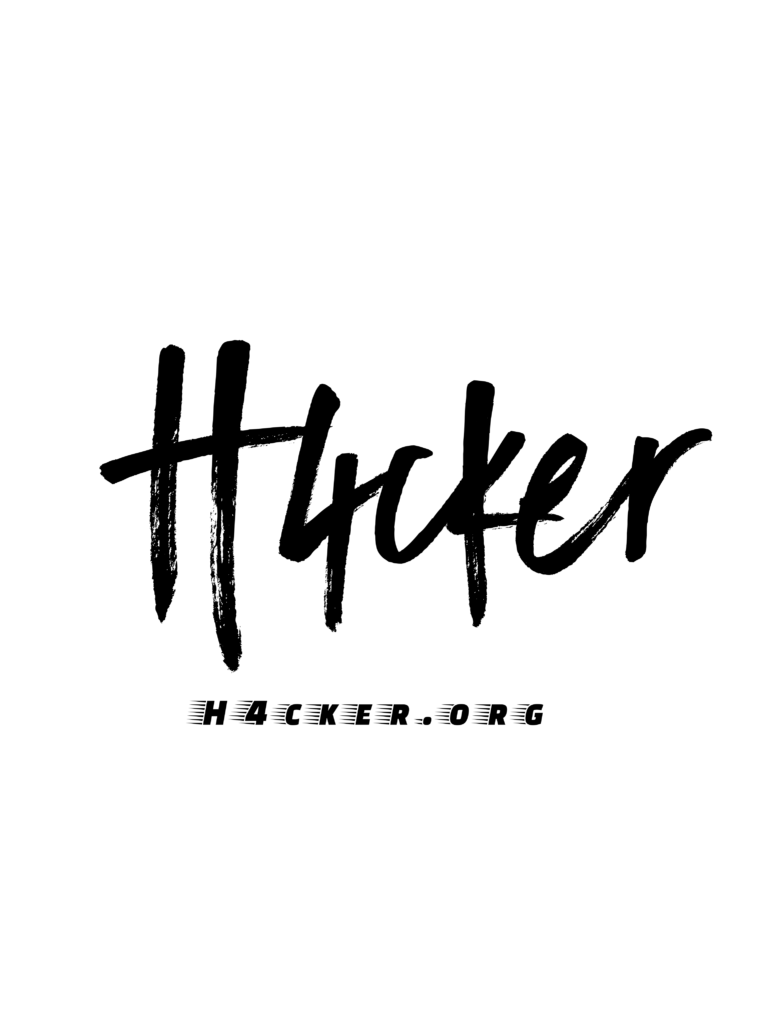
5. MISP
It stands out as a Malware Information Sharing Platform.
This project is used for collecting, storing, distributing and sharing cybersecurity indicators and threats relating to cybersecurity incidents analysis and malware analysis.
Incident analysts, security and ICT professionals or malware reversers make use of MISP to support their everyday operations in order to share structured information accurately.
In conclusion, this project is aimed at offering structured information around the security community and the world as a whole.
6. GNU Radio
This free open-source cybersecurity project brings about signal processing blocks for implementing software radios.
Most importantly, you are able to build software designed radio with the use of this and relatively cheap RF hardware.
Secondly, you can also use it to support both wireless communications research and real-world radio systems for other fields like commercial environments, academics, hobbyists, etc.

7. Malice
Malice is aimed at becoming a free open source version of VirusTotal so it can be available for everyone and companies, everywhere around the world.
You need a Docker software, 16gb disk space and a 4gb Ram to make this happen.

8. Opencti
You can use this open-source cybersecurity project to check your organization’s cyber threat intelligence knowledge and observables.
There is always a link between levels of confidence, each information, etc.
They aimed at building a standard tool so you can be able to effectively utilize technical (e.g TTPs and observables) and non-technical information (e.g suggested attribution, victimlogy etc.).

9. Computer Science Resources
This open-source cybersecurity project contains some sets of resources in many areas of computer science.
On a final note, these computer science resources are rich enough to help you in related matters.
More information
10. Pcapxray
Packet capture can be viewed as a network diagram, device identification, highlight important communication and file extraction, etc.
because of this network forensics tool.
The components of pcapxray are Network Diagram, Device/Traffic Details and Analysis, Malicious Traffic Identification and Tor Traffic GUI – a GUI with options to upload pcap file and display the network diagram.

11. Osquery
This opensource cybersecurity project view operating systems as an exceptional performing relational database.
Users are able to examine operating systems data by writing SQL-based queries because of osquery. Simple plugin and extensions API is used to bring about the SQL tables.
12. Brakeman
We all know brakeman as a static analysis security vulnerability scanner.
This tool lookout for security Vulnerabilities whenever you use Ruby programing language on Rail application.

13. Cuckoo Sandbox
In the world today, there is no better open source automated malware analysis system than the cuckoo sandbox.
If you have any file you don’t trust, looks malicious to you – give it to cuckoo sandbox, it will help you analyze to details everything about it.
14. Scumblr
You are able to do periodic syncs of data sources ( like Github repositories and URLs) and perform analysis ( like static analysis, dynamic checks, and metadata collection) on the identified results when you use this web application.
Users are able to streamline security automation because of the support scumblr has with a quite number of tasks. Via a superb automation framework to assist you in knowing, tracking, and resolving security issues quicker, scumblr streamline proactive security.

More information
15. Moloch
Moloch work is to argument users present security infrastructure in order to store and index network traffic in standard PCAP format, leading to quick indexed access. It allows you to use your best PCAP ingesting tool when analyzing workflow as moloch stores and exports all packets in standard PCAP format. It is a large scale indexed packet capture and search system.
Lastly, It can be installed on many systems you can think of.

Conclusion
Why not try out these listed and well explained opensource cybersecurity projects out to prevent your businesses and companies from every form of cyber-attacks leading to bankruptcy, etc.